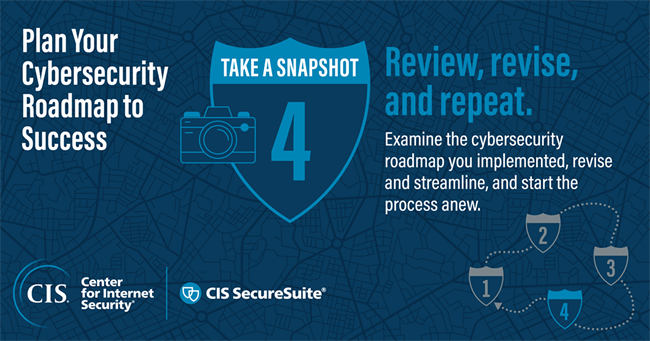
Creating a cybersecurity roadmap is a four-part journey. It begins with getting packing and figuring out what the needs are of your organization and/or your clients. From there, you plan your route by selecting a security framework as a reference point. You then hit the road and carry out that plan to achieve essential cyber hygiene.
This brings you to the last step of your cybersecurity roadmap: review, revise, and repeat. It’s here that you take a snapshot of your cybersecurity roadmap. At this point in your roadtrip, you’ve reached an attraction toward which you’ve been journeying. Doing so has changed your perspective, putting you in a position where you can examine what you’ve implemented, revise and streamline, and start the process anew onto the next attraction. In this blog post, I will discuss how you can use this last step as a means to continually strengthen your cybersecurity posture.
Evaluation: The Key to Contextualizing Implementation
Any controls plan and any risk assessment require curation not just at the beginning of implementation but through the operational lifecycle. Auditing, threat assessment, gap analysis, and changes to your organization’s infrastructure need to be ingested as part of a robust program. That’s why you need to take the time out to evaluate your efforts and measure the impact.
If you don’t, you can’t account for the dynamic array of threats and risks confronting you and/or your customers. Indeed, the consequence of “set it and forget it” has dire consequences, as the false sense of security is undermined in an ecosystem of continuous discovery and utility of vulnerabilities and threat vectors. As I said in the first installment of this series, cybersecurity is a journey, not a destination.
Evaluation serves another key function as part of your cybersecurity roadmap: it also leads into the formation of a new roadmap. Improvements and assessment will require reengineering of a controls program. Threats and risk change, and a contributing change is needed within the control infrastructure to reflect these changes.
The same can be said of business strategy and how the security program complements the business. The refinement of the roadmap reflects continuous improvement and progression though obstacles along the roadmap journey. Some can be planned along the journey, and some are surprises. Being agile enough to address each requires preparation and understanding the objectives of redefining the cybersecurity roadmap. As you account for new obstacles and requirements, you can revise your cybersecurity roadmap to take you in new directions, building upon your success as you go.

Streamline Your Cybersecurity Processes Where You Can
Given the fact that your cybersecurity journey is constantly evolving, I recommend you find areas where you can streamline your efforts. Doing so will save you time, money, and effort. You free your security professionals from tedious tasks so that they can take up more important duties.
Naturally, this affects your cybersecurity posture, too. Reducing the drag of a control will only help it integrate more fully and be accepted by your organization and respective stakeholders. If system access becomes too cumbersome or processes too inhibiting, users of the processes will find alternate ways of bypassing the controls. In essence, internally you have created a red team strategy to take a well-defined control but ultimately go backwards on the roadmap.
For example, the most secure corporate Wi-Fi has people switching to guest Wi-Fi to bypass restrictions and control, therefore wasting the time in implementation but also identifying that the control isn’t integrated with the business. Awareness becomes critical on both the implementer of the control and user of corporate system.
It might be difficult to streamline things on your own. Fortunately, the Center for Internet Security is here to help.
Our CIS SecureSuite Membership comes with tools, benefits, and resources for helping you to implement security best practices such as the CIS Critical Security Controls (CIS Controls) and the CIS Benchmarks. Take the CIS Build Kits as an example. Available as Group Policy Objects (GPOs) for Windows and Bash shell scripts for Linux, CIS Build Kits automate the “Remediation” section of the CIS Benchmarks PDF document. Such functionality helps you automate the hardening of your systems to a majority of a CIS Benchmark’s recommendations, thereby saving manual effort.
Here’s more information on how the CIS Build Kits can help you apply secure configurations.
CIS WorkBench is another Membership resource for streamlining your cybersecurity efforts. It serves as a central hub from which you can download Membership tools, resources, and benefits, including XML, Excel, OVAL, and Word versions of the CIS Benchmarks. Through CIS WorkBench, you can also tailor your CIS Benchmark settings so that you can continue your cybersecurity journey according to your unique goals.
Now through April 30, you can save up to 20% on a new CIS SecureSuite Membership using promo code “CYBER2023.” Check out our promo terms to learn more.
Navigating an Ever-Changing Destination
Cybersecurity is a journey, not a destination. The velocity of change and the ever-increased surface area of attack contributes to the narrative of continuous improvement. Adversaries will continue to attack as it is in their interests (hacktivism, nation-state, etc.) or ultimately for some adversaries (cybercriminals) a very profitable business. A similar adage is also the attacker has to be right once and the defender right all the time to address cyber risk and vulnerability.
There exists an unfair balance of defending systems compared to adversarial activity, leading us down the road of due diligence and the practice of strong cybersecurity. With that said, may this Irish blessing I’ve revised guide your cybersecurity roadmap and journey going forward:
CIS SecureSuite can guide you every step of the way from now to long into the distance, enabling you to drive your cybersecurity roadmap home. Ready to see what lies over the horizon?
Sean AtkinsonChief Information Security Officer

Sean Atkinson is Chief Information Security Officer of CIS. He uses his broad cybersecurity expertise to direct strategy, operations, and policy to protect CIS’s enterprise of information assets. His job responsibilities include risk management, communications, applications, and infrastructure. Prior to CIS, he served as the Global Information Security Compliance Officer for GLOBALFOUNDRIES, serving Governance, Risk and Compliance (GRC) across the globe.
Prior to GLOBALFOUNDRIES, Atkinson led the security implementation for the New York State Statewide Financial System (SFS) implementation from 2007 to 2014, and his last role and responsibility was as the Internal Control, Risk and Information Security Manager.
Atkinson was born in Brooklyn, N.Y. and lived in England for 18 years, graduating from Sheffield Hallam University in 2000. After moving back to the United States, he has pursued multiple degrees and certifications in the IT arena.
In addition to his work with CIS, Atkinson is also an adjunct professor of Computer Science at the College of Saint Rose.
![]()
Post Disclaimer
The information provided in our posts or blogs are for educational and informative purposes only. We do not guarantee the accuracy, completeness or suitability of the information. We do not provide financial or investment advice. Readers should always seek professional advice before making any financial or investment decisions based on the information provided in our content. We will not be held responsible for any losses, damages or consequences that may arise from relying on the information provided in our content.


