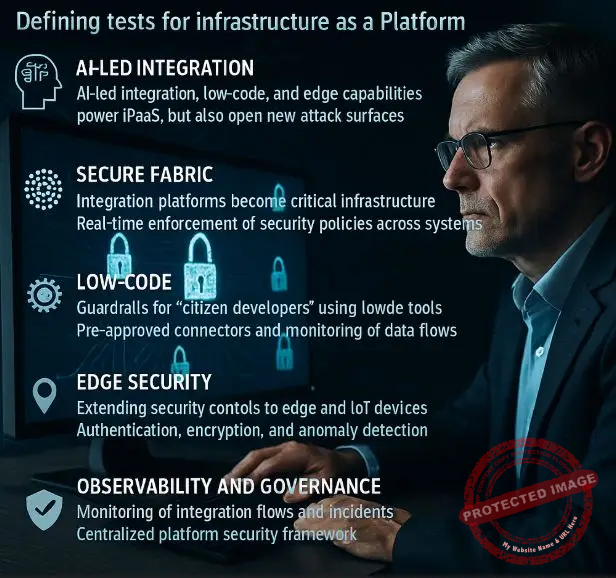
As iPaaS evolves into the central nervous system of digital enterprises, security and resilience are emerging as the defining tests for “infrastructure as a platform” in 2026. The same AI, low-code, and edge capabilities that make integration platforms powerful also open new attack surfaces that CISOs can no longer ignore.
From secure endpoints to secure fabrics
For years, security strategy focused on hardening applications, endpoints, and perimeters. Integration engines and middleware often sat in the background, treated as plumbing rather than critical assets. That complacency is no longer viable.
The global system integration market passed 410 billion US dollars in 2024 and is forecast to more than double by 2032, with cloud-based integration and iPaaS among the fastest-growing segments.Albato A separate market outlook estimates that iPaaS alone, valued around 8 billion US dollars in 2025, could approach 60 billion by 2034.Research and Markets This capital is flowing into platforms that now mediate almost every critical business process: customer onboarding, supply chain updates, fraud checks, and AI model calls.
In 2026, that means the “platform” in Infrastructure as a Platform is the fabric that connects everything. Integration no longer just moves data; it enforces policy, orchestrates AI agents, and triggers business decisions in real time. If threat actors compromise this fabric—an API gateway, a workflow engine, an edge connector—they can potentially manipulate multiple systems in a single strike. That reality is forcing enterprises to treat iPaaS not as middleware but as Tier 1 critical infrastructure, with security controls to match.
Vendors themselves are leaning into this narrative. Integration solution reports for 2025 highlight security-driven integration, multi-cloud support, and observability as central purchasing criteria, not optional extras.Oneio Infrastructure as a Platform sits squarely at that crossroads: it must deliver seamless connectivity while acting as a trusted security enforcement layer across hybrid estates.
AI-led integration: New power, new exposure
AI-led integration is the engine that transforms today’s iPaaS into tomorrow’s infrastructure platform. Informatica, among others, describes a future where agentic AI copilots suggest mappings, design workflows, and autonomously optimize integrations across data, applications, and processes.Informatica This is more than a user interface convenience; it is a structural shift in how integrations are created and maintained.
An AI assistant integrated into iPaaS can interpret natural language directives, generate pipelines, and continuously monitor them. It can scan logs, correlate anomalies, and recommend new routes when bottlenecks appear. AI orchestration platforms and agent frameworks are emerging in parallel, coordinating fleets of specialized AI models and tools like a conductor managing an orchestra.Domo+1
Yet the security implications are significant. Recent research from Veracode found that roughly forty-five percent of AI-generated code includes security flaws, even when it appears production-ready.TechRadar If integration pipelines, transformation scripts, or policy checks are increasingly authored or modified by AI, those risks propagate into the fabric that underpins enterprise infrastructure.
In 2026, mature organizations are responding in three ways. First, they integrate security scanning and policy validation directly into the AI-assisted integration lifecycle. Every AI-generated mapping or script is automatically checked against secure coding rules, data loss prevention policies, and identity constraints before deployment.
Second, they restrict what AI agents can do. Rather than giving a copilot full rights to modify production integrations, they route AI changes through controlled promotion flows: sandbox generation, human review, automated testing, and staged rollout. The AI remains a powerful assistant, but one operating inside guardrails defined by platform engineering and security teams.
Third, they leverage AI defensively inside the same infrastructure. AI models trained on integration logs, telemetry, and attack simulations can detect unusual data flows, unexpected connector usage, or anomalous authorization patterns faster than traditional rule-based systems. In the most advanced setups, AI engines running in the platform can automatically quarantine suspicious flows or require step-up authentication before allowing risky actions to proceed.
Low-code, citizen developers and the new security debt
A key promise of Infrastructure as a Platform is democratization. Low-code and no-code interfaces on top of integration fabrics allow business users to compose workflows without writing code. By 2025, analysts estimate that a large majority of new business applications will be created using low-code or no-code tools, driven by chronic developer shortages and relentless digital demand.Boomi+1
But democratization without governance creates a new kind of technical and security debt. KPMG’s work on citizen developer enablement warns that, without strong access controls and data management, low-code platforms can expose sensitive data and generate regulatory risk.KPMG Assets Guidance from consultants and platform experts similarly stresses that governance must take center stage in any low-code program to avoid shadow IT, inconsistent architecture, and hidden vulnerabilities.Columbus Global+1 Security researchers in the OWASP community have gone further, cataloging a “Low-Code/No-Code Top 10” of common threats—ranging from authentication flaws to unsafe data handling—that can surface when citizen developers are left unsupervised.DEV Community
In 2026, Infrastructure as a Platform needs to internalize those lessons. The platform becomes the governor of what low-code builders can do. Instead of allowing arbitrary connections to any endpoint, the iPaaS layer exposes a curated catalog of pre-approved connectors, transformations, and patterns. Each “building block” encodes security requirements, such as token handling, logging rules, and data masking policies, so that even non-experts build on safe primitives.
Organizations are also establishing Centers of Excellence to oversee citizen development. These units define standards, maintain shared templates, and monitor usage analytics to spot risky patterns. Low-code projects are tagged and tracked in the same observability stack as traditional development, allowing teams to detect when an innocuous-looking low-code workflow suddenly begins to move large volumes of sensitive data across borders or into unapproved SaaS tools.
Crucially, the governance plane sits inside the Infrastructure-as-a-Platform layer, not bolted on afterward. Identity, secrets management, approvals, and audit trails are implemented once at the platform level and inherited by every low-code or AI-generated workflow. Done well, this lets enterprises scale innovation while constraining risk, turning a potential security liability into a managed asset.
Real-time data, IoT, and securing the edge-native platform
Edge integration is another frontier where Infrastructure as a Platform must prove itself in 2026. Industrial IoT platforms like Crosser emphasize hybrid-first streaming analytics and integration that can run in any cloud, on premises, or at the edge, managed from a central low-code control center.Crosser Data streaming specialists highlight how technologies such as Apache Kafka and Flink enable continuous processing pipelines that bridge operational technology (OT) and IT, powering use cases from predictive maintenance to supply chain visibility.Kai Waehner
Cloud providers are also pushing real-time analytics to the edge. Microsoft’s Stream Analytics on IoT Edge lets manufacturers analyze sensor data near machines and issue low-latency commands when anomalies appear, improving both safety and uptime.Microsoft Learn PubNub and similar platforms provide low-latency publish–subscribe channels to move data between edge devices and cloud services in near real time.PubNub
In this environment, Infrastructure as a Platform stretches from central data centers to factory floors, vehicles, and retail locations. Security controls must follow. That means authenticating edge gateways as first-class identities, encrypting data streams end to end, and enforcing least privilege on which pipelines can access which topics or device groups.
A compromised edge integration node could otherwise alter sensor readings, suppress alarms, or inject falsified commands into control systems. In manufacturing or energy environments, such attacks are not just data incidents but physical safety risks.
Forward-looking organizations are therefore converging IT and OT security principles within their integration platforms. They deploy zero-trust architectures where no edge connector is automatically trusted, even if it sits on corporate networks. They segment streaming topics, constrain routing rules, and rely on the platform’s observability to detect deviations in device behavior or traffic patterns. By tying edge analytics and security into the same Infrastructure-as-a-Platform layer, they avoid mismatched policies between cloud apps and physical operations.
Observability, governance and shared responsibility for the platform
The complexity of modern integration fabrics makes transparency non-negotiable. iPaaS providers and analysts alike emphasize observability, centralized management, and multi-cloud visibility as must-haves for 2025 and beyond.Oneio+1 In 2026, observability in Infrastructure as a Platform goes beyond simple logs or metrics. It includes full lineage of data flows, dependency maps between applications, and policy evaluation traces showing why a particular request was allowed or blocked.
This level of insight underpins both security and resilience. When an incident occurs—say, an unexpected spike in calls to a payment API from a newly created low-code app—platform teams can quickly trace where that app lives, what connectors it uses, which data it accessed, and which identities executed the flow. Regulatory obligations like incident reporting or audit evidence become easier to satisfy when the integration fabric itself can provide time-stamped, tamper-resistant records.
Governance frameworks sit alongside observability. Enterprises are formalizing which roles can create connectors, approve new AI-assisted workflows, or promote edge pipelines from test to production. They are codifying data residency, retention, and encryption requirements as policies enforced by the platform.
Shared responsibility is the implicit contract. Vendors are expected to provide secure-by-default runtimes, patch supply chains, and robust identity integration. Customers are responsible for defining policies, segmenting environments, and training citizen developers. Partners—whether AI orchestration providers or streaming vendors—must integrate with the platform’s security and observability hooks, not sidestep them.
As more Infrastructure-as-a-Platform components are delivered as managed cloud services, this shared responsibility model becomes the backbone of trust. The organizations that succeed will be those that treat platform security not as a checklist but as an evolving discipline, continuously updated as new capabilities like agentic AI or quantum-ready APIs enter the mix.
Closing thoughts and looking forward
Infrastructure as a Platform in 2026 is where security, AI, low-code, and edge integration collide. It is no longer enough for integration solutions to simply connect systems; they must do so in ways that are demonstrably secure, governed, and resilient under stress.
The incentives are aligning. Market growth in iPaaS and integration platforms is strong.Research and Markets+1 AI-led integration and orchestration promise dramatic productivity gains.Informatica+1 Low-code and citizen development offer a path to scale innovation beyond traditional development teams.Boomi+1 Edge and real-time data open new opportunities for operational efficiency and differentiated customer experiences.Crosser+1
Yet each of these advances introduces fresh exposure. AI-generated code carries hidden vulnerabilities.TechRadar Low-code apps can leak data if poorly governed. Edge connectors can become back doors into sensitive environments.
Treating Infrastructure as a Platform as a premier security domain, rather than a peripheral one, is the path forward. That means investing in platform engineering teams that understand both integration and security, building CoEs for citizen developers, and insisting that every new feature—whether an AI copilot or a quantum-ready connector—ships with built-in security and governance hooks.
Looking ahead, the organizations that thrive will be those that combine bold experimentation with disciplined control. They will let AI help design integrations, but never abdicate human oversight. They will empower citizen developers, but only within a strongly governed platform. They will push integration to the edge, but keep zero trust at the core.
In short, they will recognize that the infrastructure they are building is not just a technical convenience. It is the platform on which their digital resilience, regulatory compliance, and competitive edge will rest for the next decade.
References
“AI-Led Integration: 6 Emerging Trends Shaping the Future of iPaaS” – Informatica – https://www.informatica.com/blogs/ai-led-integration-6-emerging-trends-shaping-the-future-of-ipaas.html Informatica
“Application Integration Trends for 2025” – Boomi – https://boomi.com/blog/application-integration-trends-for-2025/ Boomi
“Integration Solution Trends and Statistics in 2025” – ONEiO – https://www.oneio.cloud/blog/state-of-integration-solutions Oneio
“Citizen Developer Enablement – Low-Code/No-Code Platforms” – KPMG – https://assets.kpmg.com/content/dam/kpmg/ae/pdf-2022/03/KPMG-Low-Code-Citizen-Developer-Enablement.pdf KPMG Assets
“IoT Edge Stream Analytics – Industrial IoT Solutions” – Crosser – https://crosser.io/solutions/industry-40/iot-edge-stream-analytics/ Crosser
Benoit Tremblay, Author, IT Security Management, Montreal, Quebec.
Peter Jonathan Wilcheck, Co-Editor, Miami, Florida.
#InfrastructureAsAPlatform #iPaaSSecurity #AIPoweredIntegration #LowCodeGovernance #CitizenDevelopers #EdgeSecurity #RealTimeStreaming #HybridCloudSecurity #ZeroTrustIntegration #PlatformEngineering
Post Disclaimer
The information provided in our posts or blogs are for educational and informative purposes only. We do not guarantee the accuracy, completeness or suitability of the information. We do not provide financial or investment advice. Readers should always seek professional advice before making any financial or investment decisions based on the information provided in our content. We will not be held responsible for any losses, damages or consequences that may arise from relying on the information provided in our content.



 AMD
AMD TMC
TMC IE
IE MSI
MSI NOK
NOK DELL
DELL ECDH26.CME
ECDH26.CME