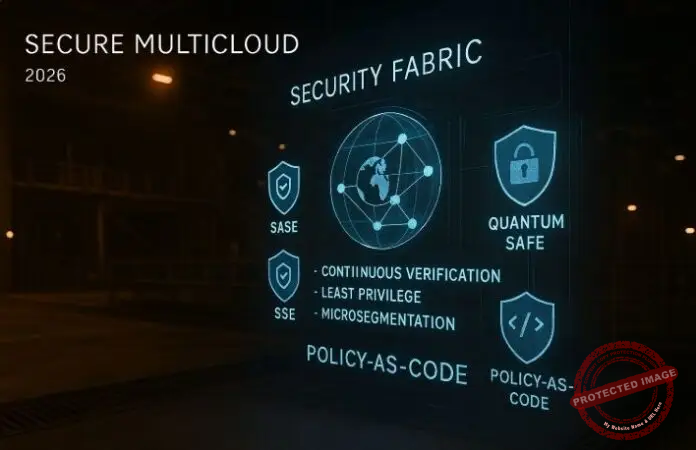
In 2026, the biggest evolution in multicloud networking is not just faster links or smarter routing. It is the way security becomes a first-class, policy-driven fabric that spans every cloud, every edge, and every identity. As enterprises adopt AI-driven automation, edge computing, and platform engineering, their multicloud networks turn into the backbone of digital operations—and adversaries follow that backbone everywhere it goes. The response is a decisive shift to zero trust, unified security dashboards, and long-term planning for quantum-safe encryption.
From scattered controls to a unified security fabric
For much of the cloud era, security controls followed infrastructure silos. Each hyperscaler offered its own security groups, firewalls, identity systems, and monitoring tools. On-premises networks added additional appliances and consoles. The result was a patchwork of overlapping policies that were hard to audit and easy to misconfigure, especially once workloads began to span multiple clouds.
As multicloud adoption grows, this fragmentation becomes untenable. Hybrid cloud security management, as practitioners now describe it, is explicitly about unifying security policies and tools to create a consistent security posture across private, public, and on-premises environments. www.firemon.com That unified posture is not just a convenience. It is the only way to maintain visibility and control when application components move between providers, edge locations come and go, and AI workloads spin up and down in response to demand.
In 2026, leading organizations are consolidating security policy and enforcement across multicloud environments into a single fabric. Instead of configuring each environment separately, they define high-level policies—who can access what, under which conditions, and from where—and push those policies into the network, identity, and application layers through centralized control planes. Multicloud networking becomes the distribution mechanism for those decisions, ensuring that every packet, connection, and API call is evaluated consistently, regardless of which provider carries it.
Zero trust becomes the default multicloud posture
Zero trust has moved from buzzword to baseline expectation. Analysts and practitioners now describe zero-trust architecture as a replacement for perimeter-based defenses, built on the principle of “never trust, always verify.” It eliminates implicit trust assumptions by requiring continuous verification of every user, device, and transaction, with identity-centric controls across the identity, device, network, workload, and data pillars. wiz.io
In a multicloud context, this means security policy cannot be tied to IP ranges or data center boundaries. Instead, policy is attached to identities—human users, service accounts, workloads—and enforced everywhere these identities operate. Devices and workloads must prove their posture and integrity before gaining access. Micro-segmentation becomes the default, limiting the blast radius of any compromise.
Vendors are responding with zero trust reference architectures explicitly designed for hybrid and multicloud environments. These architectures unify identity providers, network access controls, and workload protection platforms into coherent designs that can be deployed across multiple clouds. Cloud-native firewalls, identity-aware proxies, and micro-segmentation tools now plug into multicloud networking fabrics via APIs, allowing policy decisions to follow workloads as they scale horizontally, migrate between providers, or burst to the edge.
Crucially, zero trust in 2026 is not a single product but an operating model. Multicloud networking teams collaborate with identity, endpoint, and application security squads to define shared policy-as-code. These policies are then enforced in the fabric, with AI-driven engines monitoring behavioral signals to spot deviations—suspicious lateral movement, anomalous device behavior, or unusual cross-region access patterns—and adapt access decisions in real time.
Unified security dashboards and single-pane-of-glass visibility
All of this intent-driven security is impossible without clear visibility. That is why “single pane of glass” platforms are taking center stage in multicloud security operations. Unified network management dashboards, as described in recent analyses, reduce tool sprawl, improve visibility, and strengthen zero trust implementations by providing a centralized view of IT operations and access controls. Cloudi-Fi
These platforms ingest data from cloud-native firewalls, web gateways, identity providers, endpoint agents, and multicloud networking fabrics. They present a live, contextual map of assets, relationships, and policies: which workloads are talking to which, under what policies, and how those flows change over time.
Some architectures go further by building a graph-centric view of multi-cloud resources, effectively creating a real-time operational graph that spans every environment. Commentators argue that this kind of unified resource graph could unlock transformative visibility, governance, and automation capabilities in a world where multicloud complexity keeps rising. cloud13.ch Such graphs allow security and networking teams to explore their environment semantically: querying for “all internet-exposed services serving regulated data” or “all paths from a developer laptop to production databases.”
For day-to-day operations, unified dashboards also become the cockpit for incident response. When an alert fires, teams no longer pivot between five different consoles to understand blast radius. They can see the affected identities, workloads, and network paths in one place, then use AI-assisted tools to simulate the impact of proposed policy changes before applying them across clouds. This radically reduces the mean time to understand and the mean time to contain incidents.
SASE and SSE: Security woven into the multicloud edge
The perimeter has not disappeared; it has multiplied. Users access applications from everywhere, applications are distributed across multiple clouds, and data now flows through edge locations and 5G networks as much as traditional data centers. In this world, Secure Access Service Edge (SASE) and its close cousin, Secure Service Edge (SSE), are emerging as the de facto approach to delivering consistent security controls wherever access occurs.
SASE, as defined by leading vendors, is a cloud-delivered framework that converges networking and security into a unified platform. It combines SD-WAN capabilities with secure web gateways, firewalls-as-a-service, cloud access security brokers, and zero trust network access to provide secure connectivity for users and devices regardless of location. Cisco+1 Guidance from central cloud and platform providers emphasizes how SASE and SSE can be used to deploy zero trust strategies across hybrid and multicloud networks, unifying policy enforcement and monitoring across environments. Microsoft Learn
In practice, SASE and SSE act as security “waypoints” in the multicloud fabric. Traffic from users, branch sites, and edge devices is steered through nearby points of presence where identity, device posture, and content are evaluated before being forwarded to applications in any cloud. This replaces a patchwork of VPNs and on-premises appliances with globally distributed, cloud-native enforcement points.
By 2026, enterprises are integrating SASE platforms tightly with their multicloud networking stacks and identity systems. Policy definitions—such as which users can access which SaaS apps, which device risk scores are acceptable, and how data should be inspected or tokenized—are authored centrally and pushed to SASE points, cloud-native firewalls, and internal service meshes in concert. This unified approach dramatically reduces the chance of misaligned policies between remote access, internal apps, and multicloud workloads. Seraphic Security
Preparing for quantum-era threats with crypto agility
While day-to-day security concerns still revolve around phishing, ransomware, and misconfigurations, strategic security planning now has to account for quantum computing. Even though today’s quantum chips are far from being able to break mainstream encryption, agencies and standards bodies are clear that organizations need to begin preparing for a “Q-day” when quantum systems can defeat commonly used public-key algorithms. The Guardian+2Financial Times
The U.S. National Institute of Standards and Technology has already finalized an initial set of post-quantum encryption algorithms designed to withstand quantum computer attacks, along with new federal information processing standards for quantum-safe schemes. NIST+2NIST CSRC+2 Industry analyses note that NIST’s announcement of FIPS 203, 204, and 205 in 2024 marks a turning point: the world now has standardized building blocks for quantum-resistant cryptography, and organizations should begin planning migrations. DigiCert
For multicloud networking, the key concept is crypto agility. Architectures must be designed so that cryptographic algorithms, key sizes, and protocols can be upgraded across multiple providers and edge environments without disrupting operations. That implies centralized certificate and key management, robust inventory of where cryptography is used, and policy-driven control over which algorithms are allowed in which contexts.
In 2026, forward-looking enterprises are using their multicloud security dashboards to map out crypto dependencies, classify them by sensitivity and exposure, and define phased migration plans. AI-driven tools help identify weak or legacy cryptography embedded in older services and third-party components. Multicloud networking fabrics, SASE platforms, and application gateways are evaluated not only on current encryption support but also on their roadmap for post-quantum algorithms. The goal is to ensure that when quantum-safe standards are widely implemented, the network can adopt them quickly and consistently across all clouds and edges.
Operationalizing policy-as-code across every cloud
Underneath zero trust, SASE, and quantum-safe planning lies a common operational shift: treating security and networking policies as code. Policy-as-code frameworks allow teams to define access rules, segmentation models, and encryption requirements in human-readable, version-controlled files. These policies are then validated, tested, and deployed through automated pipelines, just like application code.
Platform and security teams in 2026 are increasingly aligning their policy-as-code efforts with multicloud management platforms that already provide unified interfaces for deployment and scaling. Multi-cloud management platforms such as those highlighted in recent overviews—spanning Kubernetes-based solutions and management layers from major vendors—show how a single interface can manage applications across providers; the same principle is now being extended to security policies. Northflank
AI and generative models play a growing role in this workflow. They assist in translating high-level regulatory or business requirements into concrete policy templates, scanning policy repositories for misconfigurations or conflicts, and suggesting incremental changes that improve security without breaking existing applications. Before any change is rolled out globally, it can be tested against simulated traffic and compliance checks within a staging environment.
By tightly tying policy-as-code to multicloud networking control planes, organizations regain a measure of simplicity in an otherwise complex world. Instead of managing hundreds of separate firewall rule sets and ACLs, they manage a smaller number of well-structured policies that are automatically propagated and enforced across clouds, SASE edges, and on-prem assets. This is the operational backbone that makes zero trust and quantum-safe strategy more than just PowerPoint concepts.
Closing thoughts and looking forward
Security has always been the constraint in ambitious IT architectures, and multicloud is no exception. What changes in 2026 is that security finally becomes an integrated, programmable layer of the multicloud fabric rather than a bolted-on set of point solutions. Zero trust principles are codified and enforced across every cloud and edge. Unified dashboards give teams the visibility they need to act with confidence. SASE and SSE bring consistent policy enforcement to wherever access occurs. Policy-as-code practice keeps everything auditable and automatable. And long-term planning for quantum-safe cryptography ensures that the protections built today will hold up against tomorrow’s threats.
Enterprises that embrace this model will treat multicloud networking as their security nervous system: continuously sensing, evaluating, and responding to risk across every environment. Those that remain stuck in fragmented, perimeter-centric approaches will find it harder to support AI workloads, edge deployments, and regulatory expectations without increasing their attack surface. The next decade will make clear that in multicloud networking, security is not just a requirement—it is the differentiator that enables innovation at a global scale.
References
What Is Zero Trust Architecture? A Complete Guide for 2025 – Wiz – https://www.wiz.io/academy/zero-trust-architecture wiz.io
Single Pane of Glass: Complete Guide to Unified Network Management – Cloudi-Fi – https://www.cloudi-fi.com/blog/single-pane-of-glass-complete-guide Cloudi-Fi
Secure Networks with SASE, Zero Trust, and AI – Microsoft Learn – https://learn.microsoft.com/en-us/security/zero-trust/deploy/networks Microsoft Learn
Hybrid Cloud Security Management: Unified Security Policies – FireMon – https://www.firemon.com/blog/hybrid-cloud-security-management-unified-security-policies/ www.firemon.com
NIST Releases First 3 Finalized Post-Quantum Encryption Standards – NIST – https://www.nist.gov/news-events/news/2024/08/nist-releases-first-3-finalized-post-quantum-encryption-standards NIST
Co-Editor, Benoit Tremblay, IT Security Management, Montreal, Quebec;
Peter Jonathan Wilcheck, Co-Editor, Miami, Florida.
#MultiCloudNetworking #ZeroTrust #UnifiedSecurity #SASE #SSE #SinglePaneOfGlass #QuantumSafeEncryption #PolicyAsCode #CloudSecurity #HybridCloud
Post Disclaimer
The information provided in our posts or blogs are for educational and informative purposes only. We do not guarantee the accuracy, completeness or suitability of the information. We do not provide financial or investment advice. Readers should always seek professional advice before making any financial or investment decisions based on the information provided in our content. We will not be held responsible for any losses, damages or consequences that may arise from relying on the information provided in our content.



 AMD
AMD TMC
TMC IE
IE MSI
MSI NOK
NOK DELL
DELL ECDH26.CME
ECDH26.CME